6.7 KiB
1883 - Pentesting MQTT (Mosquitto)
🎙️ HackTricks LIVE Twitch Wednesdays 5.30pm (UTC) 🎙️ - 🎥 Youtube 🎥
-
Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
-
Discover The PEASS Family, our collection of exclusive NFTs
-
Get the official PEASS & HackTricks swag
-
Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
-
Share your hacking tricks by submitting PRs to the hacktricks repo and hacktricks-cloud repo.
Basic Information
MQTT stands for MQ Telemetry Transport. It is a publish/subscribe, extremely simple and lightweight messaging protocol, designed for constrained devices and low-bandwidth, high-latency or unreliable networks. The design principles are to minimise network bandwidth and device resource requirements whilst also attempting to ensure reliability and some degree of assurance of delivery. These principles also turn out to make the protocol ideal of the emerging “machine-to-machine” (M2M) or “Internet of Things” world of connected devices, and for mobile applications where bandwidth and battery power are at a premium.
Default port: 1883
PORT STATE SERVICE REASON
1883/tcp open mosquitto version 1.4.8 syn-ack
Inspecting the traffic
MQTT brokers send a CONNACK packet in response to a CONNECT packet. The return code 0x00 indicates the credentials are valid and the return code 0x05 indicates they aren't. 0x05 example:
Brute-Force MQTT
Pentesting MQTT
Authentication is totally optional and even if authentication is being performed, encryption is not used by default (credentials are sent in clear text). MITM attacks can still be executed to steal passwords.
To connect to a MQTT service you can use: https://github.com/bapowell/python-mqtt-client-shell and subscribe yourself to all the topics doing:
> connect (NOTICE that you need to indicate before this the params of the connection, by default 127.0.0.1:1883)
> subscribe "#" 1
> subscribe "$SYS/#"
You could also use https://github.com/akamai-threat-research/mqtt-pwn
You can also use:
apt-get install mosquitto mosquitto-clients
mosquitto_sub -t 'test/topic' -v #Subscriribe to 'test/topic'
Or you could run this code to try to connect to a MQTT service without authentication, subscribe to every topic and listen them:
#This is a modified version of https://github.com/Warflop/IOT-MQTT-Exploit/blob/master/mqtt.py
import paho.mqtt.client as mqtt
import time
import os
HOST = "127.0.0.1"
PORT = 1883
def on_connect(client, userdata, flags, rc):
client.subscribe('#', qos=1)
client.subscribe('$SYS/#')
def on_message(client, userdata, message):
print('Topic: %s | QOS: %s | Message: %s' % (message.topic, message.qos, message.payload))
def main():
client = mqtt.Client()
client.on_connect = on_connect
client.on_message = on_message
client.connect(HOST, PORT)
client.loop_start()
#time.sleep(10)
#client.loop_stop()
if __name__ == "__main__":
main()
More information
from here: https://morphuslabs.com/hacking-the-iot-with-mqtt-8edaf0d07b9b
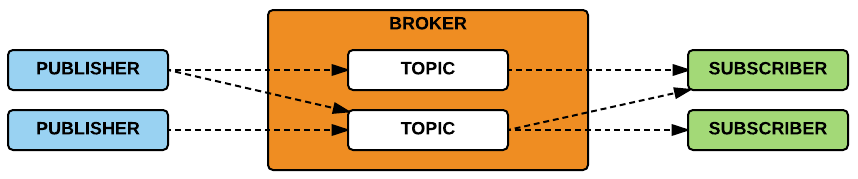
The Publish/Subscribe Pattern
The publish/subscribe model is composed of:
- Publisher: publishes a message to one (or many) topic(s) in the broker.
- Subscriber: subscribes to one (or many) topic(s) in the broker and receives all the messages sent from the publisher.
- Broker: routes all the messages from the publishers to the subscribers.
- Topic: consists of one or more levels that are separated by a a forward slash (e.g., /smartshouse/livingroom/temperature).
Packet Format
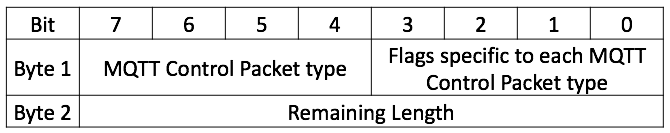
Every MQTT packet contains a fixed header (Figure 02).Figure 02: Fixed Header
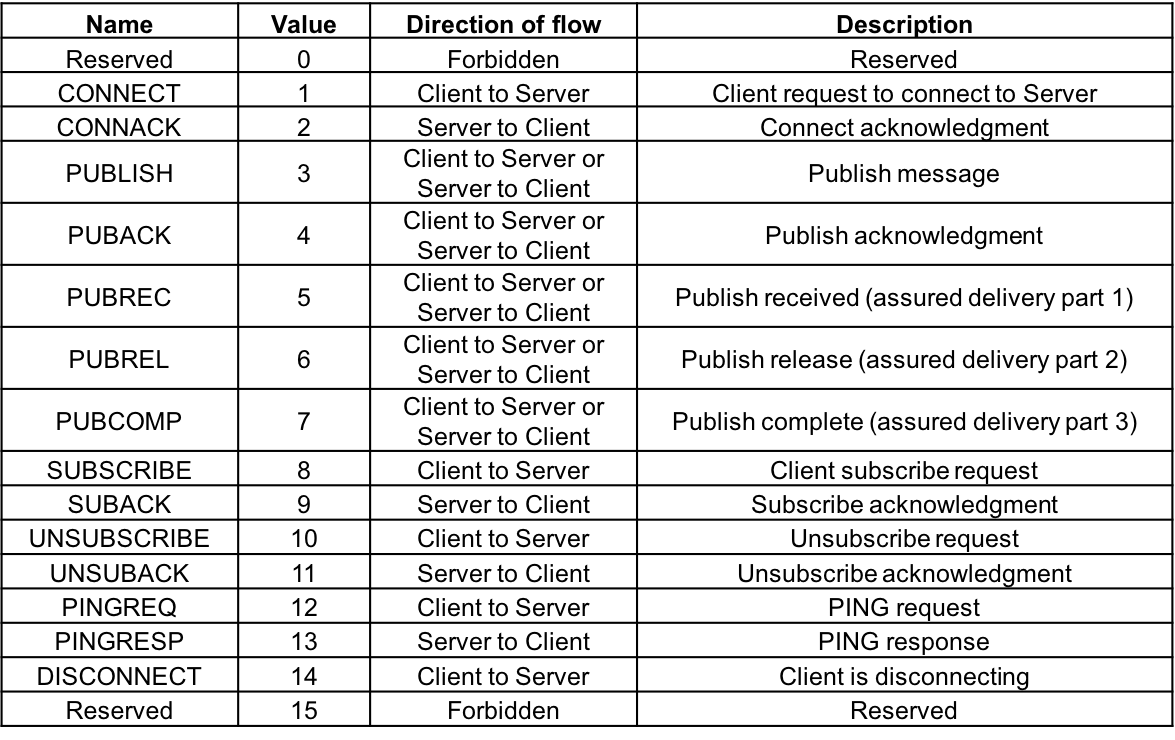
The first field of the fixed header represents the type of the MQTT Packet. All packet types are listed in table 01.Table 01: MQTT Packet Types
Shodan
port:1883 MQTT
🎙️ HackTricks LIVE Twitch Wednesdays 5.30pm (UTC) 🎙️ - 🎥 Youtube 🎥
-
Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
-
Discover The PEASS Family, our collection of exclusive NFTs
-
Get the official PEASS & HackTricks swag
-
Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
-
Share your hacking tricks by submitting PRs to the hacktricks repo and hacktricks-cloud repo.